Origin story
I got pulled into security and systems engineering by practical problems: networks that failed at the worst moment, deployments that took forever, and tooling that was powerful but painful. The more I worked on those problems, the more I liked the mix of deep technical detail and real-world consequences.
My path wasn't direct. I started in signal processing and neural networks at Lockheed Martin, building sonar feature extraction algorithms and simulating massive cyber ranges. The research was interesting, but I wanted to build things that shipped — systems that real people depended on.
That led me to offensive security tooling, then to platform engineering, then to building my own products. Each step taught me something the previous one couldn't: research taught rigor, offense taught empathy for attackers, platforms taught operational reality, products taught the cost of complexity.
These days I build automated platforms that scale without adding headcount. The thread through all of it: I like understanding how systems actually work, not just how they're supposed to work.
Philosophy
Learn in public
Sharing work-in-progress invites correction earlier, which is usually cheaper than confident silence. I write about things I'm figuring out, not just things I've mastered. The mistakes are part of the record.
Build for operators
If the person on call can't reason about it at 2 AM, it's not done. I optimize for debuggability over cleverness. The best security controls are the ones people actually use because they're not painful.
Failure is data
Mistakes are expensive only when you hide them. I write postmortems for my own projects, even when no one's watching. The pattern recognition from documented failures is worth more than the ego protection of forgetting them.
The workshop
My actual setup, not an aspirational one.
Environment
- Pop!_OS on a System76 Bonobo WS — plenty of RAM and cores for VMs
- Vim + tmux for most editing; VS Code when I need visual debugging
- GitLab for everything — repos, CI/CD, issue tracking
Lab
- KVM/QEMU with virt-manager — the native Linux choice
- Isolated VLANs for malware analysis and exploit development practice
Workflow
- Hypothesis → prototype → break it → write down what failed → repeat
- Heavy use of Ansible for anything I might do twice
- Notebook-driven debugging: timestamped logs of what I tried and why
Debugging
- strace and ltrace before reaching for a debugger
- tcpdump/Wireshark for anything network-related, even when I think I know the answer
- git bisect for regressions; printf debugging when I'm impatient
Non-technical interests
The stuff that isn't on a resume but shapes how I think.
Family
Married with three small kids. Most of my free time is hikes through Manassas Battlefield, cushion forts, Dr. Seuss, Star Wars, and hide-and-seek. We speak Portuguese at home; my wife is from Brazil.
Languages
I speak Imerina Malagasy from my LDS mission in Madagascar. In 2008 I interpreted English to Malagasy for a live conference broadcast.
Running
7 marathons finished. Member of the Marine Corps Marathon Runners Club.
Other pursuits
Eagle Scout. Motorcycle enthusiast: Honda Shadow Spirit VT1100C.
NAME
steven - chief architect and platform engineer
SYNOPSIS
steven [--security] [--automation] [--scale] [--leadership]
DESCRIPTION
Chief Architect. Founder of Stormblest. Builds automated platforms for cybersecurity and infrastructure.
OPTIONS
--security
Architecture that thinks like an attacker. CISSP + eCXD + OSCP.
--automation
2-hour deploys, not 2-week projects. Infrastructure-as-code.
--scale
50+ environments from one codebase. Customers self-serve.
--leadership
Lead from the front. Share the wins, own the losses. Mistakes are tuition, surprises are debt. Speak up early and we'll figure it out.
SEE ALSO
Credentials
Education
M.S. Computer Science
Georgia Institute of Technology
B.S. Electrical Engineering
Brigham Young University
Security certifications
CISSP
Certified Information Systems Security Professional
Broad security management certification covering 8 domains.
Valid through Sep 2027
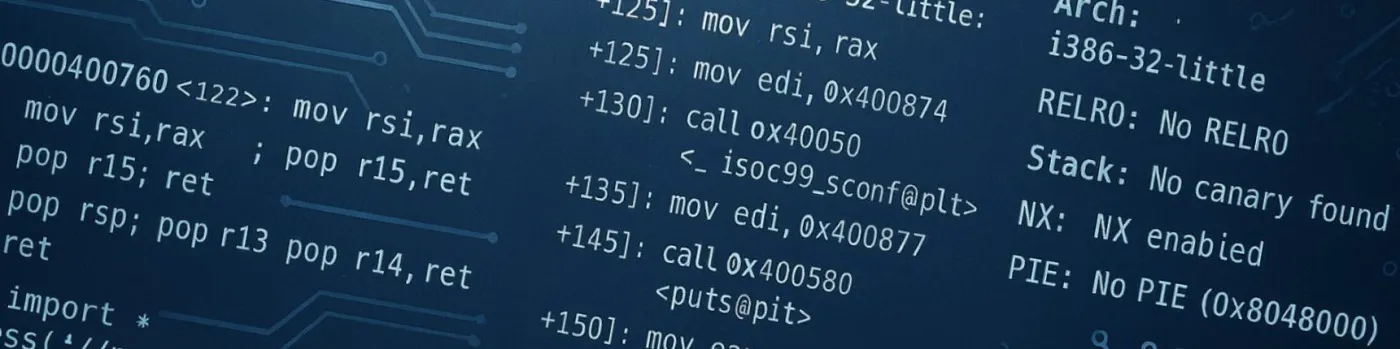
eCXD
eLearnSecurity Certified eXploit Developer
Advanced exploit development on 32-bit and 64-bit Windows and Linux: bypassing DEP/NX, ASLR, SafeSEH, Stack Canaries.
OSCP
Offensive Security Certified Professional
Hands-on penetration testing under time constraints.
OSWP
Offensive Security Wireless Professional
Wireless network security assessment and exploitation.
Clearance
Former TS/SCI (2010–2023)
Amateur radio
Amateur Extra — KW4TD
Work history 15+ years
rimstorm-inc Rimstorm, Inc. | bash 2021 – Present
$ cat rimstorm.log
Chief Technology Officer
Herndon, VA
- Architected GovCon Enclave — secure collaboration platform achieving CMMC Level 2 compliance
- Built automation framework reducing enclave deployment from 2 weeks to 2 hours
- Scaled to 50+ production enclaves supporting hundreds of users
- Led platform through first successful C3PAO CMMC Level 2 certification
stormblest Stormblest | bash 2019 – Present
$ ./mistborn --status
Founder / Principal Engineer
- Created Mistborn — open-source zero-trust networking platform
- Built on Debian + WireGuard with Nextcloud, Jitsi, Vaultwarden
- Designed reproducible deployments for non-specialist admins
redlattice REDLattice | bash 2018 – 2021
$ strings redlattice.bin
Senior Software Engineer
Chantilly, VA
- Binary analysis and automation pipelines for cyber operations
- Linux environments for developers in classified settings
mantech-card ManTech CARD | bash 2015 – 2018
$ ansible-playbook deploy.yml
Principal CNO Software Engineer
Reston, VA
- Production automation frameworks for network deployment and monitoring
- Trained customer-site engineers on secure systems
lockheed-martin-atl Lockheed Martin ATL | bash 2009 – 2015
$ python3 research.py --extract features
Research Scientist (Engineering Leadership Development Program)
Manassas & Arlington, VA
- Neural networks for sonar feature extraction; submitted IP on novel architectures
- Engineered cyber ranges of 10,000+ virtual and physical nodes
- Special Recognition Awards (2012, 2014, 2015)
Say hello
I'm always happy to talk about security architecture, systems design, or whatever you're building. If you found something useful here, or if you think I got something wrong, I'd like to hear about it.
Get in touch