Security Architect
I build private AI tools, ship open-source projects, and break the rest.
Fifteen years building production systems, including GovCon Enclave, the platform behind Rimstorm's acquisition, plus the projects, field notes, and open-source tools that I built along the way.
stevenfoerster.com | bash
last login: today on tty1
sf : ~ $ whoami
steven // builder // architect // security engineer
sf : ~ $ help
Try: `whoami`, `contribute`, `fortune`, `man sf`, `easter-egg --konami`
interactive mode: type `help`
Projects & Open Source
What I'm building
Security and privacy tools, open-sourced. Each one started as a problem I needed to solve.
Open Source
Solux
Local-first AI workflow engine that chains inputs, transforms, and local LLM steps into automated pipelines. Everything runs on your machine.
Why I built it
I wanted composable AI workflows without cloud APIs, vendor lock-in, or data leaving the network.
Explore SoluxOpen Source
Butler
Access-control reverse proxy for Ollama. Multi-user auth (API keys, JWT, OIDC), per-user model policies, rate limiting, and Prometheus observability.
Why I built it
Shared Ollama instances needed authentication, authorization, and rate limiting without changing Ollama or clients.
View ButlerOpen Source
TrueStream
Real-time deepfake detection for video calls. A browser extension that runs local ONNX inference on Meet, Teams, and Zoom with a five-level trust ladder.
Why I built it
Video call impersonation is a real threat and existing tools require cloud inference. This runs entirely in the browser.
View TrueStreamOpen Source
Porthole
Sandboxed captive portal browser for Android. Authenticates with hotel and airport WiFi without breaking your VPN kill switch.
Why I built it
VPN kill switches and captive portals are mutually exclusive on Android. Porthole bridges the gap with a time-limited, sandboxed session.
View PortholeIn development since 2019
Keystone
Sovereign identity and policy management. A self-hosted stack that unifies directory, single sign-on with MFA, mesh networking, and a compliance engine, aiming to replace AD, Entra ID, Intune, and Always-On VPN.
Why I built it
Identity and device compliance should not depend on a single vendor cloud, pricing model, or jurisdiction.
Follow the buildActive Build
Vinsium
Private AI infrastructure that runs entirely on your network. Zero-trust mesh networking, a local AI workflow engine, and enterprise identity. No cloud dependency.
Why I built it
I wanted organizations to run real AI workloads without sending sensitive data off-network.
Follow the buildPast project
Mistborn
Open-source privacy platform built to make WireGuard and self-hosted services approachable on commodity hardware.
Why I built it
I built it to protect real systems without demanding enterprise budgets.
Origin storyLab highlights
Interactive labs
Interactive demos built to make difficult concepts obvious through experimentation.
Tutorials
Hands-on guides
Step-by-step walkthroughs covering exploit development, AI red teaming, Android security, and systems engineering.
Run a Private AI Assistant in Your SOC
Build a RAG pipeline over Wazuh alerts that helps analysts triage incidents without sending data to external services.
Binary Function Similarity with Graph Neural Networks
Represent disassembled functions as control flow graphs, train a graph neural network for similarity embeddings, and apply it to patch diffing.
Tuxscope Lab 7: Profiling Disk I/O Latency with eBPF HashMaps
Use eBPF HashMap state to trace the block layer and measure per-request I/O latency from issue to completion.
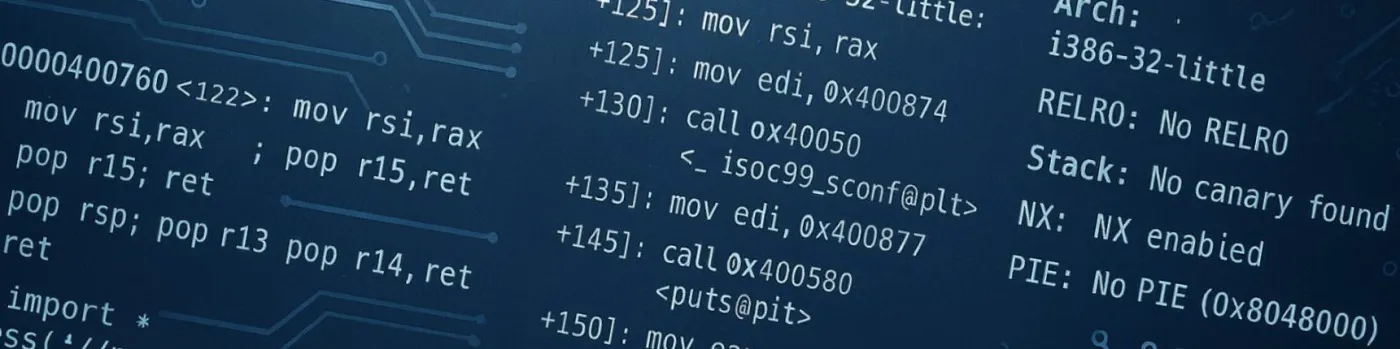
Bypassing GCC Stack Canaries on Linux
Defeat -fstack-protector by leaking canaries via format strings, brute-forcing them across forks, and overwriting __stack_chk_fail in the GOT.
A WireGuard Road-Warrior VPN on OpenWrt
Set up a full-tunnel WireGuard VPN on OpenWrt so your laptop and phone route securely home from anywhere, in its own firewall zone, with IPv6.
Threat Intelligence Extraction with Named Entity Recognition
Fine-tune a BERT token classifier to extract IOCs, threat actors, and techniques from security reports, then wrap it in a structured extraction function.
Building a Tool-Calling Agent with RAG
Build a RAG pipeline with ChromaDB, implement a ReAct-style tool-calling agent, and measure retrieval with precision, recall, MRR, and nDCG.
RAG Poisoning: How Adversarial Documents Break Retrieval Pipelines
Understand how hidden instructions, topic hijacking, and authority impersonation attacks break RAG pipelines, and build defenses against them.
Tuxscope Lab 6: Observing Memory with Page Fault Tracing
Trace page faults and OOM kills to understand how Linux implements virtual memory through demand paging.
Encrypted Traffic Classification
Classify application types and detect malicious channels in TLS-encrypted traffic using only flow metadata, with a 1D CNN and a gradient boosting baseline.
System Prompt Extraction and Defense Hardening
Techniques for extracting hidden system prompts from LLM applications, and how to harden your prompts against extraction attacks.
Format String Vulnerabilities on x86
Exploit printf-family functions when user input is the format argument: leak stack values, dump memory at arbitrary addresses, and write a byte into the GOT.
SPI and JTAG Flash Dumping from Hardware
Identify SPI flash chips, dump them with a CH341A programmer or in-circuit SOIC clip, and use OpenOCD over JTAG to extract firmware with no removable chip.
WebView and Hybrid App Vulnerabilities
Exploit JavaScript bridges, file access misconfigurations, and cross-site scripting in Android WebViews, one of the most common bug classes in mobile apps.
Adversarial Evasion of ML Security Classifiers
Attack the malware classifier from Part 3 with gradient-based adversarial perturbations, measure evasion rates, and build defenses with adversarial training.
Windows CFG and Hardware-Enforced Stack Protection (CET)
How Control Flow Guard validates indirect call targets, why it cripples JOP on Windows 8.1+, and how Win11 hardware shadow stacks layer on via Intel CET.
DNS Exfiltration Detection with Sequence Models
Build an LSTM that detects DNS tunneling and data exfiltration by analyzing sequences of DNS queries, and compare against a per-query feature baseline.
Secure Boot and Firmware Integrity Verification
Implement a verified boot chain on embedded Linux with U-Boot FIT image signing, then attack it: downgrade attacks, unsigned image rejection, and bypasses.
Tool Use and Agentic Exploitation
Attack LLM agents through confused deputy problems, tool argument injection, and data exfiltration via tool chains, with hands-on Ollama exercises.
Connect Your RAG Pipeline to Live CVE Feeds
Pull from the NVD API and OSV.dev, implement incremental ingestion, and add metadata filtering to your local RAG pipeline.
Local RAG with PDF Documents
Parse PDFs, handle tables and layout-aware chunking, extract metadata, and feed structured content into your local RAG pipeline.
Add a Chat Interface to Your Local RAG Pipeline
Wrap your local RAG pipeline in a Streamlit chat UI with conversation history, streaming responses, and source citations that show where every answer came from.
Chain-of-Thought and Reasoning Evaluation
Compare direct and chain-of-thought prompting on math, implement self-consistency via majority voting, and evaluate code generation with Pass@K.
Attack Surface Mapping: Intents, Content Providers, and Deep Links
Enumerate an Android app's exposed components: exported activities, services, content providers, broadcast receivers, and deep link handlers.
Phishing URL Detection with Fine-Tuned Transformers
Fine-tune a DistilBERT model to classify phishing vs legitimate URLs, compare against a TF-IDF baseline, and explore tokenization challenges with URL strings.
Exploiting an Embedded Service: Buffer Overflow on ARM
Cross-compile a vulnerable network daemon for ARM, exploit a stack buffer overflow with ARM-specific techniques, and build ARM ROP chains in a QEMU/GDB lab.
Dynamic Analysis with Frida
Use Frida to hook Java and native methods at runtime, bypass SSL pinning, and observe Android app behavior live on a device or emulator.
Tuxscope Lab 5: Tracing Process Lifecycle with eBPF
Trace fork, exec, and exit events in real time to understand how Linux creates, transforms, and destroys processes.
APK Structure, Decompilation, and Static Analysis
Tear apart an Android APK, the manifest, DEX bytecode, resources, and native libraries, and learn to spot vulnerabilities without running the app.
Android Bug Bounty Lab Setup
Build an Android security testing environment with an emulator, rooted device, ADB, and the essential reverse engineering and dynamic analysis toolchain.
Windows Kernel Pool Overflow Foundations with HEVD
Trigger and analyze a pool buffer overflow in a vulnerable Windows kernel driver, groom the kernel pool, and map the privilege-escalation stage that follows.
Network Intrusion Detection with Autoencoders
Build a PyTorch autoencoder trained only on normal network flows to detect intrusions as high-reconstruction-error outliers, and compare with Isolation Forest.
Malware Classification with Neural Network Embeddings
Train a feedforward neural network in PyTorch to classify PE files from static features, and compare deep learning against tree-based methods for tabular data.
Bypassing ASLR on Windows
Defeat Windows ASLR with non-ASLR modules, partial pointer overwrites, and information leaks to build reliable exploits against randomized address spaces.
Preference Tuning with DPO
Implement the third stage of LLM training: train a reward model on preference pairs, run DPO to align without reinforcement learning, and compare to best-of-N.
Tuxscope Lab 4: Network Monitoring
Monitor TCP connections in real time by probing tcp_v4_connect and inet_csk_accept, capture source and destination IPs, ports, and connection direction.
Indirect Prompt Injection Through Untrusted Data
Explore how adversarial content in retrieved documents, emails, and web pages can hijack LLM behavior, from RAG poisoning to cross-plugin attacks.
Tuxscope Lab 3: File I/O Observation
Probe the VFS layer with kprobes on vfs_read and vfs_write to observe per-process file I/O volume in real time.
Efficient Fine-Tuning with LoRA and Quantization
Fine-tune a language model with LoRA on a fraction of the parameters, compare FP32/FP16/INT8/NF4 inference, and weigh Flash Attention's memory-compute tradeoff.
Bypassing DEP with ROP on Windows
Build a ROP chain on Windows to bypass Data Execution Prevention, using mona.py to find gadgets and VirtualProtect to mark shellcode executable.
UART and Serial Console Exploitation
Identify and interact with UART interfaces on embedded devices using QEMU, extract boot logs, interrupt U-Boot for a root shell, and dump flash over serial.
Tuxscope Lab 1: Hello eBPF
Build your first eBPF program in Rust, trace write syscalls and stream events from kernel space to userspace with PerfEventArray.
Tuxscope Lab 2: Syscall Tracing
Trace all system calls in real time, capture syscall IDs from raw_syscalls/sys_enter, resolve them to names, and switch from PerfEventArray to RingBuf.
Jailbreaking: Bypassing LLM Alignment Controls
A taxonomy of jailbreak techniques: persona attacks, encoding tricks, few-shot poisoning, and multi-turn escalation, with a rubric for scoring bypasses.
LLM Decoding and Prompt Strategies
Compare greedy, beam search, top-k, and nucleus decoding on GPT-2, visualize MoE routing, and test zero-shot, few-shot, and chain-of-thought prompting.
BERT Fine-Tuning and Position Embeddings
Explore encoder-only transformers through BERT: inspect masked-LM predictions, fine-tune on sentiment, compare position embeddings, and benchmark distillation.
Tokenization and Attention from Scratch
Build the four foundational transformer components from scratch in NumPy: tokenization, word embeddings, self-attention, and positional encoding.
Transformers & LLMs: Series Introduction and Environment Setup
An overview of the Transformers and LLMs series: what it covers, who it is for, how the companion code is structured, and how to set up your environment.
Multi-Tenant GPU Isolation
Analyze GPU isolation (MIG, MPS, vGPU, time-slicing) from an offensive angle, mapping the attack surface of shared GPUs and what leaks across tenant boundaries.
Prompt Injection from First Principles
Build a vulnerable LLM chatbot with Ollama, exploit it with direct and indirect prompt injection, then layer defenses to see why it is fundamentally hard.
Ollama: Run LLMs Locally
Install and manage local LLMs with Ollama: CLI usage, model management, Modelfiles, the REST API, tool-calling models, Open WebUI, and coding-tool integration.
Linux Exploitation Lab Setup
Build and run the vulnerable binaries used throughout the Linux Exploitation Fundamentals series, in Docker or natively.
LLM Tokens, Context Windows, and the Attack Surface
How LLMs process text through tokenization, manage context windows, and where these mechanics create exploitable attack surface for red teamers.
WebMCP Attack Surfaces
Build a web app that exposes tools to AI agents via WebMCP, then demonstrate tool poisoning, schema mismatch, response injection, and cross-tool exfiltration.
Container Escape: Namespace and Privilege Breakouts
Exploit four container escape techniques, privileged mounts, Docker socket abuse, namespace escapes, and cgroup release_agent, then harden against each one.
Training a ROP Gadget Classifier with XGBoost
Build a machine learning classifier that predicts whether a ROP gadget is useful for exploit chains, using features extracted from x64 disassembly and XGBoost.
Embedded Linux Attack Surface Analysis
Build a stripped embedded Linux image with Buildroot, then audit open ports, syscalls, suid binaries, kernel modules, and writable paths, and harden it.
Firmware RE with Binwalk and Ghidra
Extract firmware from an IoT update file, unpack the filesystem, identify interesting binaries, and reverse engineer them in Ghidra to find bugs.
Cross-Compiling with Buildroot and QEMU
Set up an embedded Linux dev environment: build a custom ARM image with Buildroot, boot it in QEMU, and remotely debug binaries with GDB. No hardware required.
Anomaly Detection on Linux Audit Logs
Build a lightweight anomaly detection pipeline that flags suspicious Linux sessions using auditd logs, feature engineering, and scikit-learn; no GPU required.
Build a Local RAG Pipeline with Ollama and ChromaDB
A hands-on guide to building a retrieval-augmented generation pipeline that runs entirely on your machine, using security advisories as the knowledge base.
Writing Your First Wazuh Custom Decoder and Rule
A step-by-step guide to writing custom Wazuh decoders and rules, from reading a raw syslog line to triggering an alert.
Recovering from a Pop!_OS Kernel Panic on System76
Step-by-step recovery for a Pop!_OS kernel panic after an interrupted update.
Windows Egghunter Exploitation
Use egghunter shellcode to locate and execute a larger payload when buffer space is limited.
Windows SEH Overflow Exploitation
Exploit Structured Exception Handler (SEH) overflows on Windows, bypassing SafeSEH protections to achieve code execution.
Windows Stack Buffer Overflow
Exploit a classic stack buffer overflow on Windows, from crash discovery to shellcode execution using Immunity Debugger and mona.py.
Remote Exploitation with Socket Reuse Shellcode
Exploit a remote x86 Linux service: leak addresses to bypass PIE, split shellcode across discontinuous buffers, and reuse the socket to evade firewall rules.
Bypassing ASLR on x64 Linux
Defeat Address Space Layout Randomization by leveraging fixed addresses in the binary when PIE is disabled.
Bypassing NX with mprotect ROP Chains
Use Return-Oriented Programming to call mprotect() and make stack memory executable, then jump to shellcode on x64 Linux.
Bypassing NX with ROP on x64 Linux
Use Return-Oriented Programming to bypass NX protection on 64-bit Linux, chaining gadgets to call system() with /bin/sh.
ROP Gadget Hunting Toolkit
A practical reference for finding, filtering, and verifying ROP gadgets with ropper, ROPgadget, and GDB-PEDA, plus chaining strategies.
Stack Buffer Overflow on x64 Linux
Exploit stack buffer overflows on 64-bit Linux systems, understanding the differences from x86 including register usage and address handling.
Return-to-libc Attack on x86
Bypass NX protection by returning to libc functions instead of executing shellcode on the stack. Learn to leak addresses and chain function calls.
Redirecting Execution to Hidden Functions
Learn how to exploit a basic stack buffer overflow to redirect execution to a hidden function in a SUID binary and gain elevated privileges.
Basic Stack Buffer Overflow on x86
A comprehensive guide to exploiting stack buffer overflows on 32-bit Linux systems, from vulnerability discovery to shellcode execution.
Linux Syscalls for Exploit Development
How Linux syscalls work at the instruction level, int 0x80 vs syscall, register setup, and the key syscalls used in shellcode and ROP chains.
The Stack: Memory Layout and Function Frames
How the stack works in x86 and x64 Linux: memory layout, push/pop mechanics, function prologues and epilogues, and why overflows overwrite the return address.
x86 and x64 Registers and Calling Conventions
A practical guide to CPU registers, partial register access, flags, and how function arguments are passed on x86 and x64 Linux.
Arch Linux Installation Guide
A comprehensive guide to installing Arch Linux with full disk encryption, secure boot, and hardened security configuration.
From the notebook
Recent posts and takeaways
Build logs, deep dives, and sharp corners I wish someone had warned me about.
Writing
Original writing
Novels about cognition, identity, and what it costs to become something new.
Contemporary Problems
What the Water Carried
A neuroscientist has forty-eight days to finish work only this version of her can do.
Contemporary Problems
What the City Carried
180,000 people woke up smarter. The city wasn't built for it.